User CRUD
Feature Detail
Description
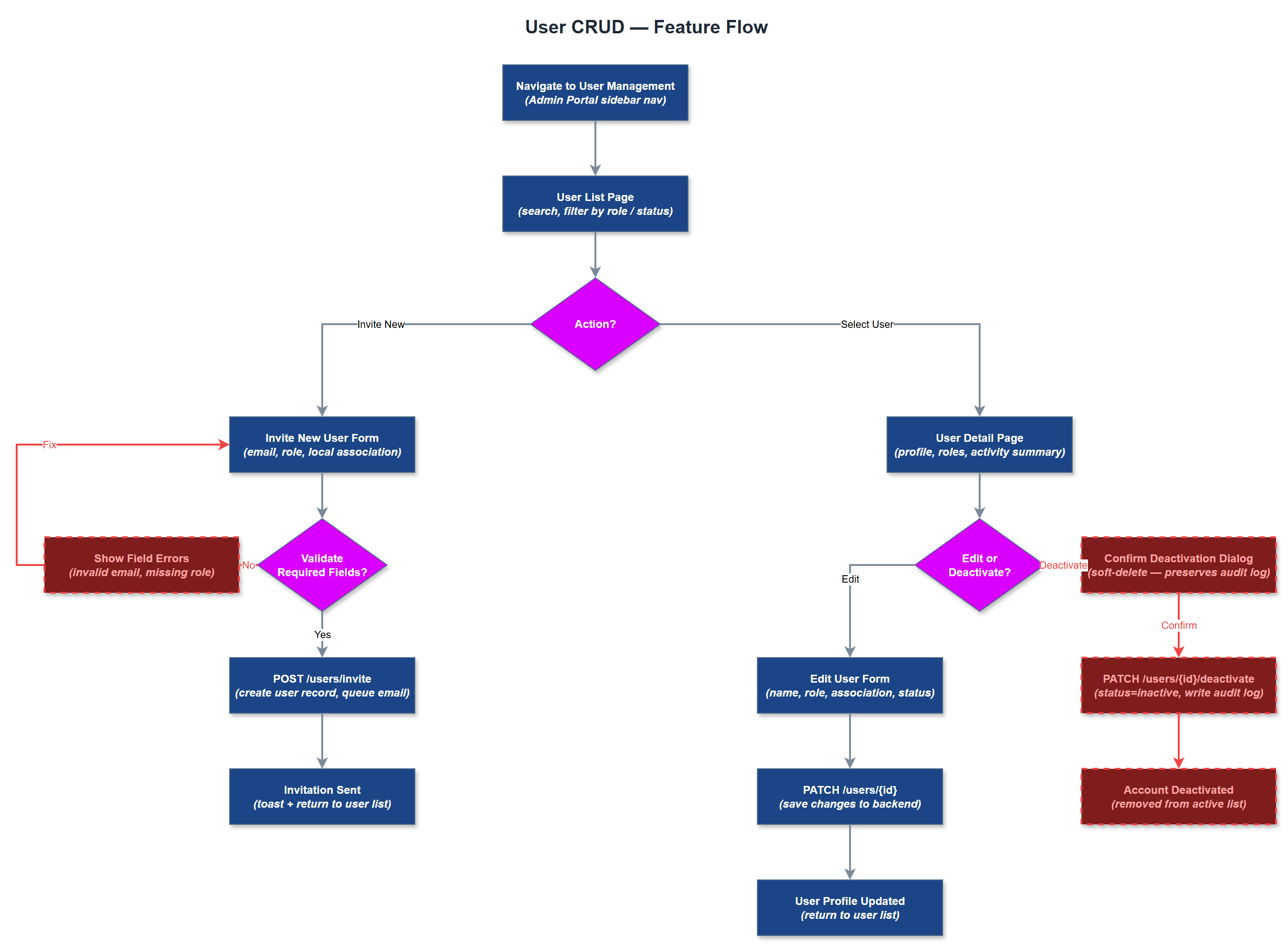
User CRUD provides the foundational capability for organization administrators to create, view, edit, and deactivate user accounts within the Admin Web Portal. Administrators can invite new peer mentors and coordinators by email, set their initial role and local association context, and manage their profile data. The feature covers the full lifecycle of a user account from invitation through active use to deactivation, without hard deletion to preserve audit integrity. The user list page presents a searchable, filterable table of all users within the administrator's organization scope, with status indicators and quick-action controls. The user detail page exposes full profile information, role assignments, activity history summaries, and account status. Editing respects multi-tenancy boundaries - org admins see only their own organization's users, while global admins have cross-organization read access for support purposes only.
User Flow
Analysis
Without the ability to manage users, no organization can onboard peer mentors or coordinators into the platform, making this feature a hard prerequisite for all operational value the platform delivers. Organization administrators currently rely on manual spreadsheets and email threads to track who is active, which role they hold, and whether they are still affiliated - a process that is error-prone and time-consuming. Replacing this with a structured admin interface directly reduces administrative overhead and ensures that access rights are always current and auditable. From a compliance and data governance perspective, maintaining accurate user records with role and organization context is essential for GDPR accountability and Bufdir reporting integrity. The ability to deactivate rather than delete users preserves the audit trail required for grant compliance, protecting the organization from liability during external reviews.
The user list and detail pages are implemented as Next.js server-rendered pages consuming the shared REST API at `/api/v1/users`. Server-side rendering ensures that sensitive user data is never exposed in client-side bundles. Invitation flow sends a tokenized email link via the notification infrastructure; the token is single-use and expires after 72 hours. Deactivation sets an `is_active` flag and invalidates all active sessions for that user via the sessions table. Multi-tenancy enforcement is applied at the API middleware layer - every request is scoped to the authenticated admin's `organization_id`, preventing cross-tenant data access regardless of query parameters. Global admin access uses a separate elevated-privilege token with explicit audit logging of every read. Pagination, search, and filtering are implemented server-side with indexed PostgreSQL queries on `users` and `user_roles` tables to support large organizations.
Components (38)
Shared Components
These components are reused across multiple features
Service Layer (9)
Data Layer (12)
Infrastructure (7)
User Stories
No user stories have been generated for this feature yet.