Session Management
Feature Detail
Description
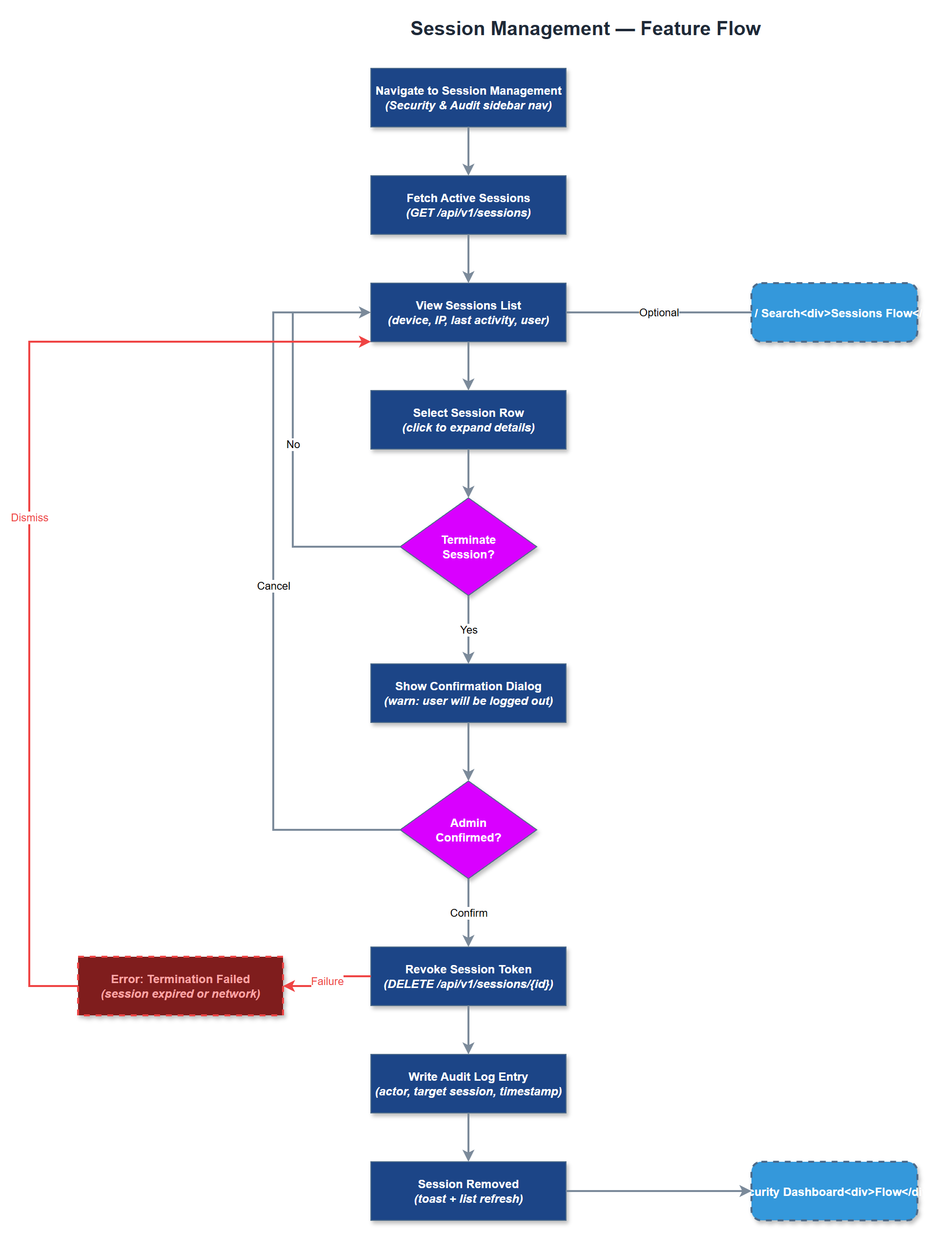
Session Management enables administrators to view, monitor, and terminate active user sessions across the Meander platform. This includes both mobile app sessions (JWT tokens stored in device Keychain/Keystore) and admin portal sessions (HTTP-only cookies). Administrators can see all active sessions for users within their organization, including device type, last activity timestamp, and IP address. The feature supports remote session termination for security incidents such as lost devices or compromised accounts, and enforces configurable session expiry policies. It integrates with the broader security posture of the platform by feeding session data to the Security Dashboard.
User Flow
Analysis
Remote session termination is a critical security control for organizations managing volunteers who may lose their devices or leave the organization unexpectedly. Peer mentors and coordinators access sensitive contact data and encrypted assignments - the ability to instantly revoke access reduces the window of exposure after a security incident. For organization administrators, session visibility provides operational assurance that only authorized individuals are actively accessing the system. This feature is particularly important for organizations with high volunteer turnover, such as HLF and NHF, where offboarding needs to be immediate and verifiable. It also supports GDPR compliance by enabling organizations to demonstrate control over data access.
Sessions are tracked in the sessions PostgreSQL table, with entries created at login and invalidated at logout or termination. JWT-based mobile sessions use short-lived access tokens (15 minutes) with longer-lived refresh tokens stored in the device's secure storage; server-side session records track refresh token hashes for revocation. Admin portal sessions use HTTP-only cookies backed by server-side session records. The session management UI in the admin portal queries active sessions scoped to the admin's organization. Remote termination marks the session record as revoked; the next token refresh attempt returns 401, forcing re-authentication. Session termination events are written to the audit log. Configurable idle timeout and absolute session lifetime policies should be stored in organization_settings.
Components (35)
Shared Components
These components are reused across multiple features
Service Layer (9)
Data Layer (12)
Infrastructure (7)
User Stories
No user stories have been generated for this feature yet.