Role-Based Access Control
Feature Detail
Description
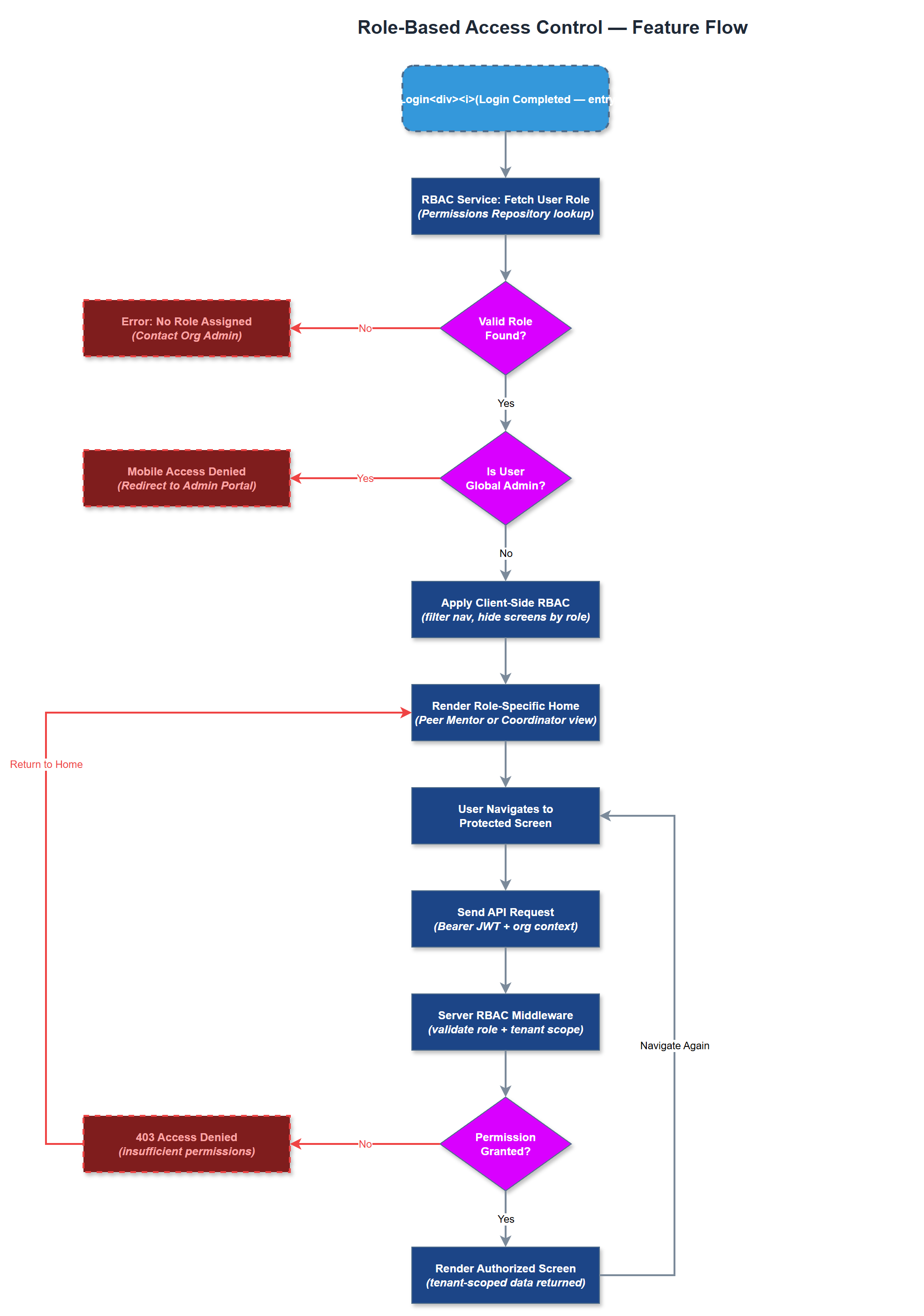
Role-Based Access Control (RBAC) enforces what each authenticated user can see and do within Meander, based on their assigned role within their organisation. The four roles - Peer Mentor, Coordinator, Organisation Admin, and Global Admin - have distinct permission sets that govern access to screens, API endpoints, and data. RBAC is enforced both on the client side (navigation and UI visibility) and server side (API authorisation middleware), ensuring tenant isolation and preventing privilege escalation.
User Flow
Analysis
RBAC is the structural backbone of the entire platform's security and multi-tenancy model. Without it, peer mentors could access coordinator functions, coordinators could modify organisation settings, and organisation data could leak across tenants - all of which would be catastrophic for GDPR compliance and organisational trust. The clearly defined role boundaries also simplify onboarding: each role sees only what is relevant to their responsibilities, directly reducing cognitive load for peer mentors with beginner-level digital skills. Global admin tenant isolation is a critical commercial requirement for selling the platform to multiple independent organisations.
Roles and permissions are stored in the PostgreSQL user_roles table, with role claims embedded in the JWT payload at login. The Next.js API uses middleware to validate role claims on every protected route. The Flutter app reads role claims from the decoded JWT to conditionally render navigation items and screens. The user_roles table supports multiple roles per user within different organisations, enabling coordinators who are also org admins in another association. A permissions matrix document should be maintained alongside the code. Role changes take effect on the next token refresh cycle; immediate revocation requires token invalidation via a server-side denylist.
Components (36)
Shared Components
These components are reused across multiple features
Service Layer (9)
Data Layer (12)
Infrastructure (7)
User Stories
No user stories have been generated for this feature yet.